ISI News
Mountain Hikes, Castle Ruins and Privacy Engineering
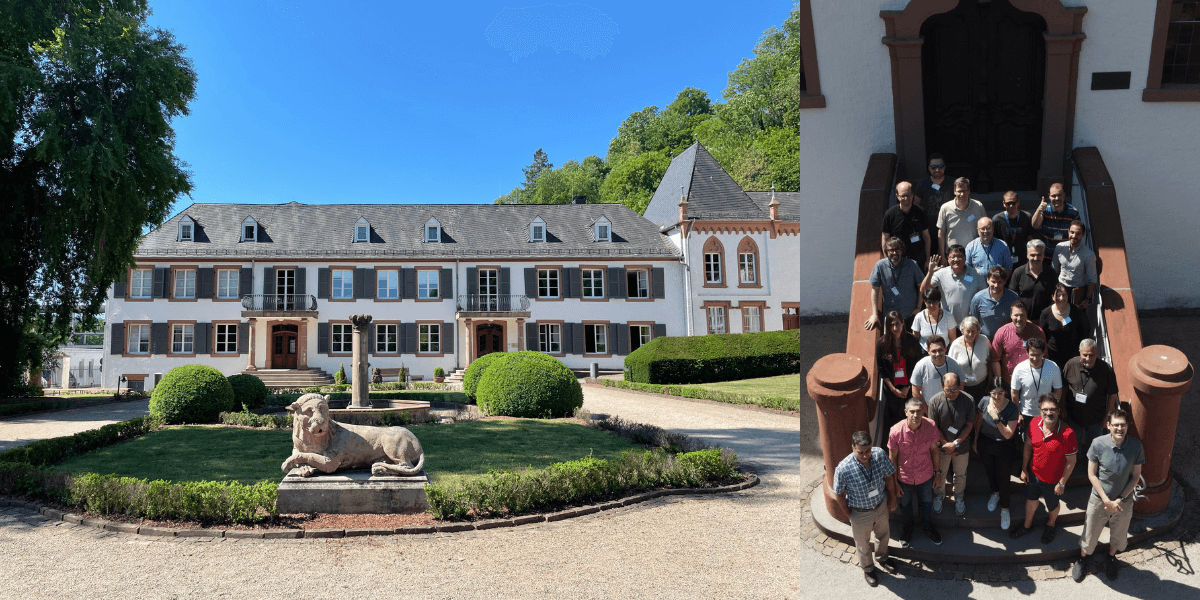
David Balenson, Senior Supervising Computer Scientist and Associate Director of the Networking and Cybersecurity Division at the USC Information Sciences Institute was recently invited to take part in a Dagstuhl Seminar in Saarland, Germany.
Dagstuhl Seminars are highly prestigious and provide a unique format and environment to focus on the exchange and development of ideas. Each week-long seminar focuses on a specific area of computing research. The topic Balenson was invited to participate in was Privacy Protection of Automated and Self-Driving Vehicles.
Assembling the Experts
The Dagstuhl Seminars are world-renowned, and spots are highly coveted. Balenson was asked to join as an expert in automotive cybersecurity. He said, “I’ve been involved in automotive cybersecurity for the past eight plus years and I currently have a National Science Foundation project about collecting automotive research data sets and sharing them with the community.” Prior to joining ISI, Balenson helped run the Automotive Cybersecurity Industry Consortium, which “brought together automotive manufacturers to pool resources, leverage them with government funding and resources, and conduct cooperative ‘pre-competitive research’ to improve the level of cybersecurity in automobiles.”
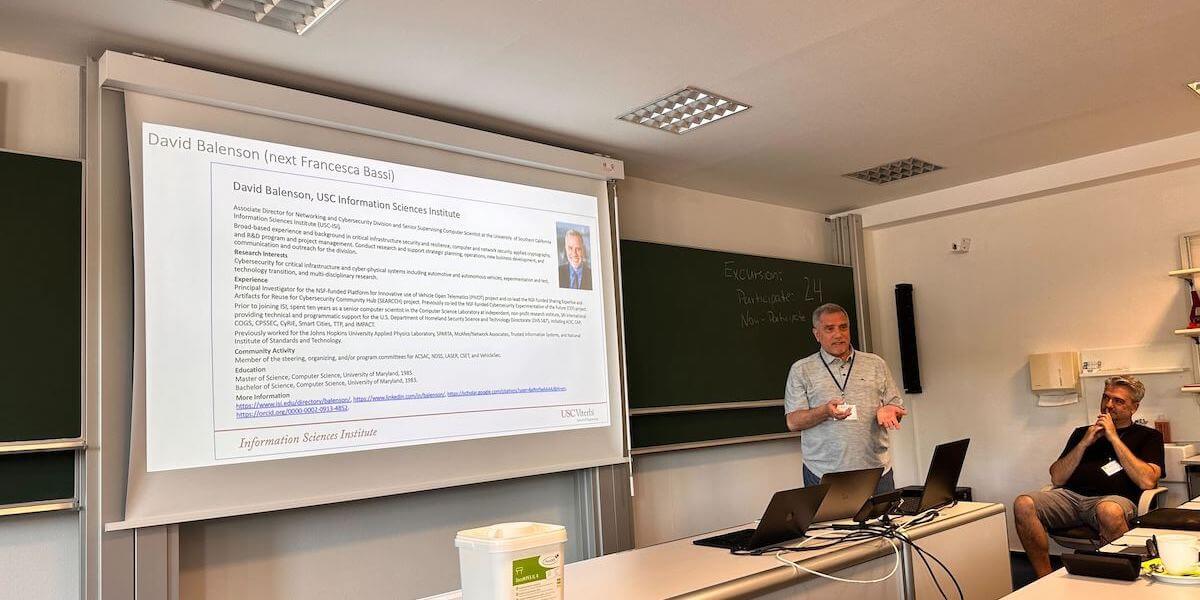
Photo Credit: Benedikt Brecht
Balenson’s seminar, however, was not made up of only automotive cybersecurity professionals. He explained, “The organizers put together a diverse set of experts who brought different perspectives. So, it was not just technical per se. There were academics, both junior and senior; there were professors, postdocs and PhD students. There were also lawyers and policy-oriented people; and automotive manufacturers, including OEMs [original equipment manufacturer] and suppliers who provide components to the OEMs.”

Photo Credit: Bryant Walker Smith
Identifying Research Challenges
The goal of the week was not to answer all the questions around the topic, but to produce a research roadmap that addresses the major hurdles the experts see in making progress on the topic. Balenson said, “We wanted to set a research agenda, come up with key priorities that the community could pursue in terms of privacy for automated and self-driving cars, and help identify some of the questions, challenges, and possible solutions around the deployment of privacy protection in these vehicles.”
What are some of the challenges that go along with privacy in autonomous and self-driving cars? The group came up with four areas to focus on:
- Data Collection and Sharing. Vehicles have become computers and networks on wheels, and they can not only collect and share data about vehicles, but also drivers, passengers, and pedestrians. Balenson said, “And the issue is, manufacturers and others are using that data. And we want to maintain privacy about who we are, what we’re doing, and where we’re going.”
- The Trade-Off Between Safety and Privacy. Balenson said, “Part of the motivation behind autonomous and self-driving vehicles sharing information is to try to maintain safe driving environments, and they have to share some amount of information for that to happen. But there’s a trade-off between sharing the information to get you safely from point A to point B and privacy. And where do you draw the line between one versus the other?”
- Privacy Engineering. This is, in general, the idea of “building privacy into the design and development of an engineered system, so it becomes an integral, inherent part of the engineering and not an afterthought,” said Balenson. And specifically to this seminar, the group looked at how privacy engineering can be applied to automated and self-driving vehicles. He explained, “How do you embed privacy strategies, privacy patterns, and privacy-enhancing technologies into an automotive product development lifecycle?”
- The Trade-Off Between Trust and Privacy. Balenson explained, “Imagine cars that are cooperating with each other and with roadside infrastructure. For example, you get to an intersection, and the cars are communicating with each other about which one should go through the intersection, and which should stop. They are ‘connected’ because they’re communicating with each other and ‘autonomous’ because they’re driving themselves. In order to do that you’ve got to have trust that all the vehicular, roadside, and communications components are all who they say they are, and that they’re doing what they’re supposed to be doing. And there can be a trade-off between sharing data to establish this trust and privacy.”
Social Events and Storied Past
The group did more than just talk about privacy. Built into the weeklong event were plenty of social gatherings. “We had meals together; we hiked up a mountain to the ruins of a castle. We toured gardens, did river tours, ate at German restaurants in town,” recounted Balenson.
One of the most lasting memories for Balenson was paging through notebooks of seminars past. He said, “There are abstract notebooks where everybody who takes part in the seminar hand signs one of the notebooks. And anybody who presents has to handwrite an abstract of their presentation. I was able to go back and look at past seminars, and I was able to find one in particular from 1997, with some famous cryptographers that I happened to know from early in my career when I worked with applied cryptography.”
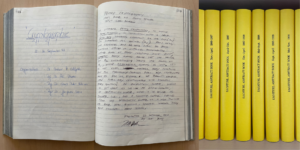
Photo Credit: David Balenson
He said of the week, “I was highly honored to be invited to participate in such a prestigious event and help form the research agenda. I formed connections with new researchers and learned ideas for future research.”
Over the years, many ISI researchers have been invited to Dagstuhl Seminars. The list includes current ISIers Yolanda Gil, Christophe Hauser, Filip Ilievski, Carl Kesselman, Clifford Neuman, Srivatsan Ravi, John Wroclawski, and even the Keston Executive Director of ISI Craig Knoblock has participated several times.
VIDEO CREDIT: BENEDIKT BRECHT
Published on
Last updated on